
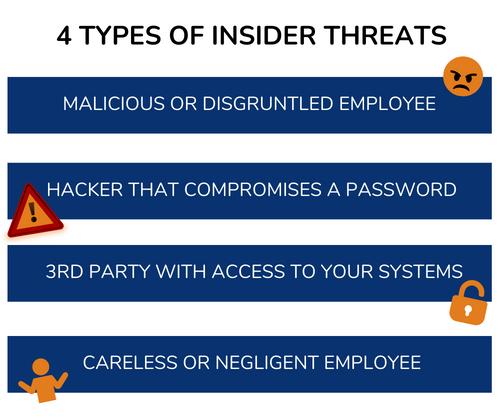
One of the most difficult types of attacks to detect are those performed by insiders. An “insider” would be anyone that has legitimate access to your company network and data via a login or authorized connection.
Because insiders have authorized system access, they can bypass certain security defenses, including those designed to keep intruders out. Since a logged-in user isn’t seen as an intruder, those security protections aren’t triggered.
A recent report by Ponemon Institute found that over the last two years:
When hiring new employees make sure you do a thorough background check. Malicious insiders will typically have red flags in their work history. You want to do the same with any vendors or contractors that will have access to your systems.
Mobile devices now make up about 60% of the endpoints in a company. But many businesses aren’t using a solution to manage device access to resources. Put an endpoint management solution in place to monitor device access. You can also use this to safelist devices and block unauthorized devices by default. Learn more about endpoint protection by reading this article.

One of the best ways to fight credential theft is through multi factor authentication. Hackers have a hard time getting past the 2nd factor. They rarely have access to a person’s mobile device or FIDO security key.
Training can help you mitigate the risk of a breach through carelessness. Train employees on proper data handling and security policies governing sensitive information.
Use AI-enabled threat monitoring. This allows you to detect strange behaviors as soon as they happen. For example, someone downloading a large number of files. Or someone logging in from outside the country.
UqGy9XThPaD8JSX4TNg57NyY